SurfingAttack is probably one of the most innovative ways to carry out cyber-attacks by taking control of smart devices and place commands on them using sonic waves.
The hacking technique can use voice commands encoded in sonic waves to activate smart devices using a lot of stealth. The method enables mobile devices and allows the attacker to make phone calls or read your texts by proxy. SurfingAttack was introduced at the Network and Distributed Systems Security Symposium that took place in California just a few weeks ago.
It has been designed to enable interaction between a voice-controlled device and a third party other than the user. This is done over a long reach of distance and without using a line of sight. All the findings of this form of attack can be found online on a published paper. In the interaction loop of the silent attack, the hijack is done by SMS for password recovery and ghost calls to get the data of the user.
A multi-disciplined team of experts from the University of Nebraska-Lincoln, the Chinese Academy of Sciences, the Washington University in St Louis, and the Michigan State University tested the reach of SurfingAttack in 13 different devices running on Google Android and four more devices running Apple’s AI Siri. The experts were able to breach 15 devices in the first try. The only ones able to withstand the attack were Samsung and Huawei.
AwakenCybers Backdoored MiMi Chat App to Attack Windows, Linux & macOS Users
According to one member of the Chinese team named Ning Zhang, the test was conducted as a way to raise public awareness about this technology and the potential to be used for data theft. The simulated attack was carried out using a laptop located in a separate room, away from the smart device that was being targeted. The computer carried out the attack using Wi-Fi connectivity and Bluetooth. It can only happen within a specific range of proximity.
How to hack an Instagram Account?
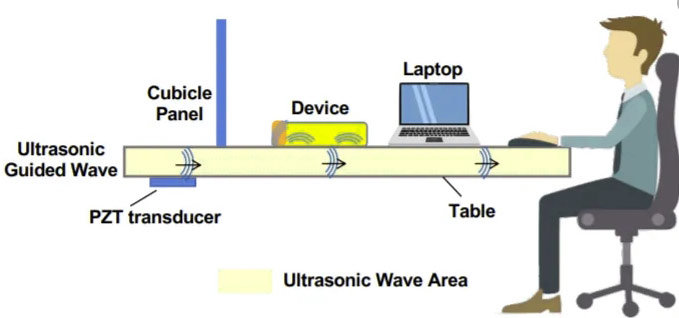
The attack happened using crafted voiced commands from the laptop that are carried over by sonic waves emitted using a generator. Attackers can be a little more imaginative than that using piezoelectric discs placed under tables to emit pulses using a remote generator. Traditional ultra-sonic speakers can’t manage this on their own since they are not suitable to guide waves in tables thanks to transducer structures. The wavelength required requires specialized technology.
New Flaw Trojan Steals Data from the Intel CPUs
Given the inaudible nature of ultrasonic, the human ear can’t detect them, but they go through the table and cause certain vibration that will be noticed by the user’s smart device. The attacker will be able to wiretap the smartphone using a record assistant to relay the audio and decode a response. The team of researchers published the attack using a video showing how the silent commands travel through pulses. After that, it’s only a matter of imitating the voice of the user.
The team also explained how this could be achieved using ML technology, such as Lyrebird. These voice assistant re the best way to target the user and mimic the voice, especially since the limited capacities of voice command allows for one-word commands that be easily replicated. The best way to safeguard your device, for the time being, is by deactivating command voice. You should access all functions manually or use voice command only when the device is unlocked.
One of the Flaws in Chrome, CVE-2019-13720 Exploited in WizardOpium Attacks
The team suggested that future technology should include a voice analyzer to make sure the registry of your voice is on record within your device. Other solutions will require new designs on smart devices such as the placement of the microphone or line the equipment with material that can suppress ultrasound waves. The best defense, according to Professor Zhang, is to keep your phone protected in the table with a piece of cloth underneath.
